ADFS Single Sign-On Support
Introduction
FileCloud offers a SAML-based Single Sign-On (SSO) service that provides customers with full control over the authorization and authentication of hosted user accounts.
Using the SAML model, FileCloud acts as the service provider and also a claims-aware application. FileCloud customers that host FileCloud can authenticate against Active Directory Federation Services (ADFS) and log in to FileCloud.
FileCloud acts as a Service Provider (SP) while the ADFS server acts as the identity provider (IdP).
Active Directory Federation Services (ADFS) Support
When SAML SSO Type is selected and ADFS is enabled in FileCloud, FileCloud will act as a Service Provider (SP) and also a claims aware application. As a claims-aware application, FileCloud accepts claims in the form of ADFS security tokens from Federation Service, and can use ADFS claims to support Single Sign On (SSO) into FileCloud. To specify the identity claims that are sent to the FileCloud refer to the IdP Configuration section below.
When ADFS is used, the IdP (Identity Provider) in this document refers to Active Directory Federation Server.
When ADFS successfully authenticates the user account, FileCloud (SP) authentication module verifies that the user account exists in FileCloud. If the user account does not exist in FileCloud, then a new user account is created and the user is logged into FileCloud.
Prerequisites
- A Working ADFS implementation. This is beyond the scope of FileCloud. Please refer to articles available on the internet on setting up ADFS.
FileCloud must be running on HTTPS using SSL. (Default Self signed SSLs that ships with FileCloud will not work). ADFS does not allow adding a relying party that is running on HTTP or self-signed SSL. You can follow the steps here to set up SSL in FileCloud.
FileCloud SSO Configuration Steps
In order to successfully configure SSO, the following steps must be followed.
- Configure Apache Webserver
- Set SAML as a the default Single Sign On Method in FileCloud Interface and Configure IdP settings in the FileCloud Admin Interface
- Enable Single Sign On Link on the login page.
- Register the FileCloud as a Service Provider (SP) with IdP by adding FileCloud as a Relying Party Trust in ADFS.
Step 1: Web Server Configuration
Follow the steps in SAML Single Sign-On Support to set up the Web Server configuration and enable SSO.
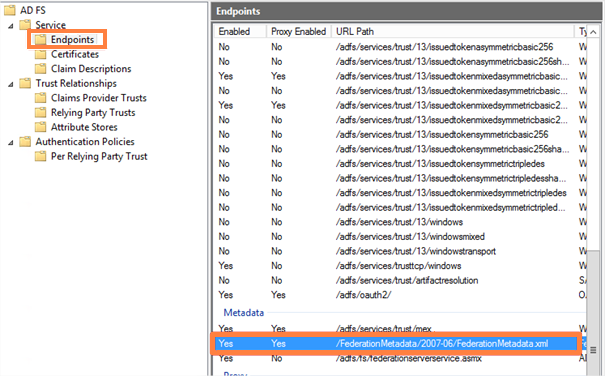
Step 2: IdP/ADFS Configuration
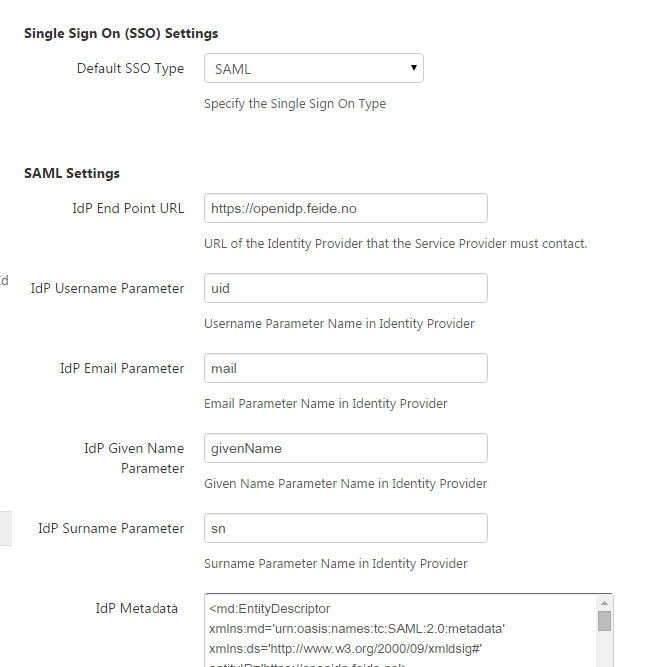
In the FileCloud Admin Interface – Settings => SSO => SSOType the default FileCloud SSO Type must be set to SAML. Other parameters must be set as per your IdP settings.
| FileCloud Parameters | ADFS as IdP Data can be obtained from Federation Metadata |
|---|---|
default SSO Type | For ADFS, select SAML |
IdP End Point URL | Identity Provider URL (Entity ID) e.g. http://yourADFSdomainName/adfs/services/trust |
Idp Username Parameter | Identifies the Username (must be unique for each user) value: uid |
IdP Email Parameter | Identifies the email of the user (must be unique) value: mail |
IdP Given Name Parameter | Identifies the given name of the user. value: givenName |
IdP Surname Parameter | Identifies the surname of the user Default value: sn |
IdP Metadata | |
Enable ADFS | Yes |
| Log Mode | Set the Log Mode for the SAML Calls. Default Value: prod (Do not use DEV for production systems) |
Step 3: Enable SSO link
Follow the steps in SAML Single Sign-On Support (under SSO Configuration Steps, Step 5) to enable SSO sign-in on the User or Admin Interface.
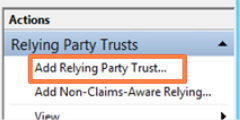
Step 4: Register FileCloud as SP in IdP/ADFS
Registering FileCloud as SP in ADFS involves series of steps from adding FileCloud as a Relying Party Trust in ADFS to setting up Claim Rules for FileCloud in ADFS. Please follow the steps below to successfully register FileCloud in ADFS.
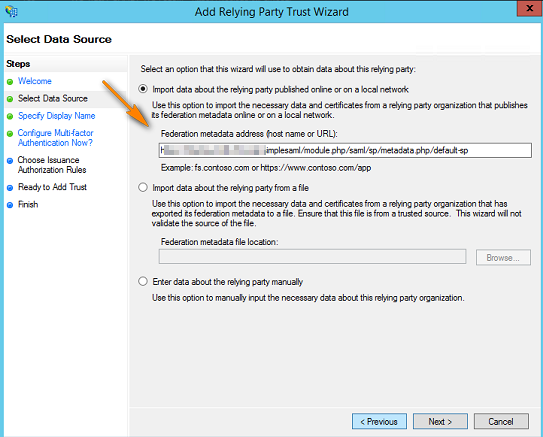
Before you proceed, you must be able to download the metadata of FileCloud from the following Entity ID URL. (Note HTTPS).
https://<Your Domain>/simplesaml/module.php/saml/sp/metadata.php/default-sp
If you have trouble downloading the metadata from the above URL, please check if HTTPS is working and all the previous steps 1, 2 and 3 above were completed successfully.
1. On your ADFS server, open the ADFS management console, expand Trust Relationships and select Relying Party Truest node. In the actions pane, click Add Relying Party Trust
2. Click Start then paste the Entity ID URL from above into the Federation Metadata address field and click Next.
you can also do it manually by downloading your metadata file from http://<your domain>/simplesaml/module.php/saml/sp/metadata.php/default-sp and import it into ADFS by choosing "import data about relying party from a file"
once you access the metadata URL you need to enter admin credentials to be able to download the metadata file, the username is admin and password can be found in :
<FileCloud WEB ROOT>/thirdparty/simplesaml/config/config.php
3. Accept the Warning
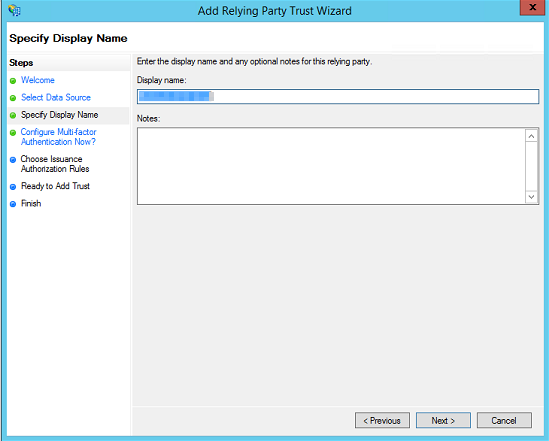
4. Enter the display name for the Relying Party Trust, usually your FileCloud URL.
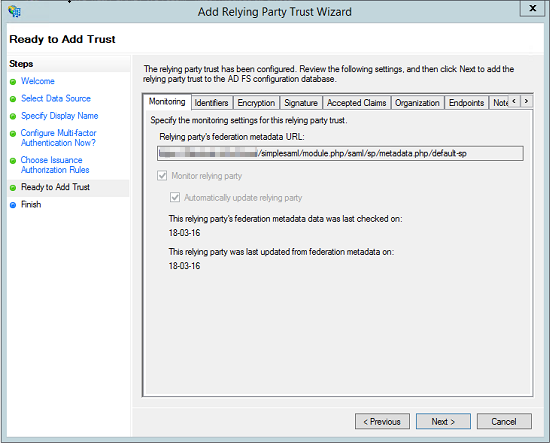
5. Next Way through your Wizard until you reach Ready to Add Trust Page. Here, review the tabs. Encryption and Signature tabs must have values associated with them.
6. Click Next and the new Relying Party Trust is now added.
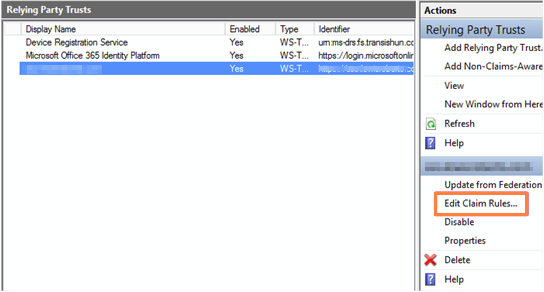
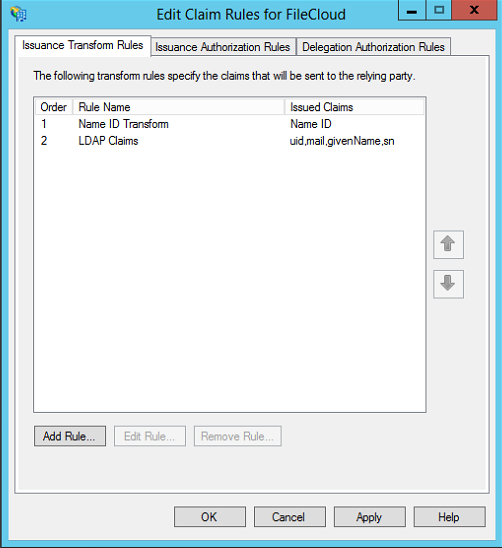
7. Select the Relying Party Trust we have just added and then click Edit Claim Rules.
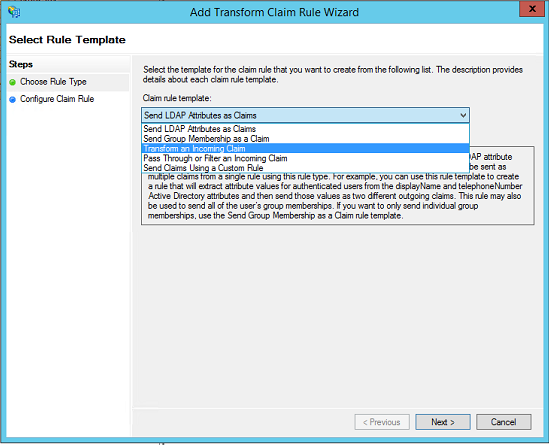
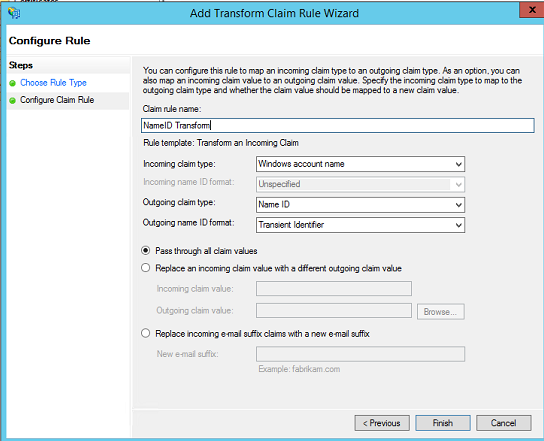
8. Add an Issuance Transform Rule. Choose the Transform an Incoming Claim rule Template.
8. Give a Claim Rule Name (Name ID Transform - can be anything). Enter Windows Account Name as Incoming Claim Type and Name ID as Outgoing Claim Type. Choose Transient Identifier for Outgoing Name ID Format. Select the radio button Pass through all claim values. Click Finish to Add the Claim Rule.
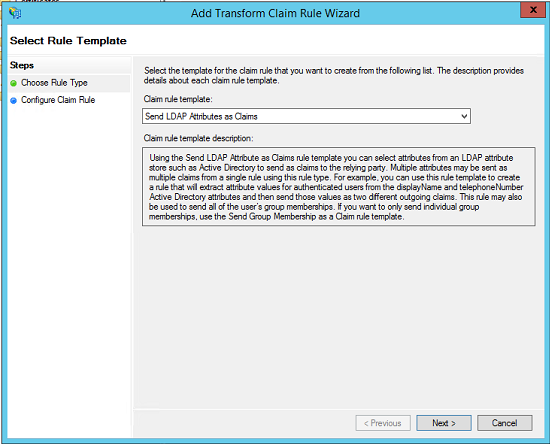
9. Add another Issuance Transform Rule. Select Send LDAPAttributes as Claims template.
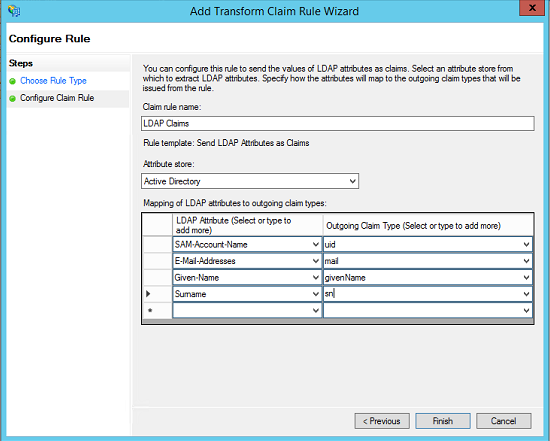
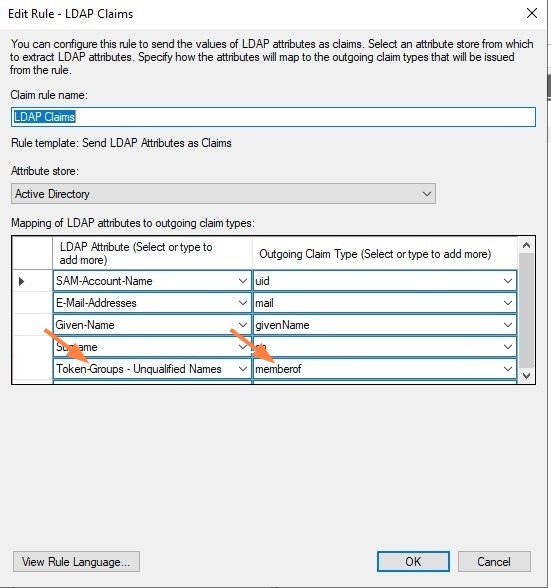
10. Fill in the rule fields:
- Enter a name for Claim Rule (LDAP Claims - can be anything).
- Select Active Directory as Attribute Store.
- Add the mapping of LDAP Attributes to outgoing claim types. The outgoing claim type must match the names as specified in FileCloud SSO Settings UI Page (the screenshot below follows the FileCloud SSO Settings as documented above).
- For Outgoing claim type, uid and mail are required. SAM-Account-Name in the screenshot below can be replaced with UPN if desired.
- For ADFS configuration, add an additional claim parameter (Token-Groups - Unqualified Names > memberof).
Click Finish to add the rule.
11. Once Configured, you should have two issuance transform rules. (Screenshot below shows only one rule. However, you will have 2 rules (Name ID Transform and LDAP Claims if followed the steps above). Click Apply and Exit.
This completes the ADFS configuration and the FileCloud is added as a Relying Party Trust in ADFS server. You can now test the SSO from FileCloud by going to the FileCloud login page and clicking the Single Sign On link as mentioned in Step 3 of this documentation.
Troubleshooting
Please check the troubleshooting section from SAML Single Sign-On Support (under SSO Configuration Steps, Step 8) .